Nov 27, 2023 | News, Cyber Security
In the contemporary era of digital advancements, the landscape of potential threats has undergone transformations, with ransomware emerging as a particularly formidable cyber menace. This malicious software poses a substantial risk to individuals, businesses, and...

Sep 25, 2023 | News, Cyber Security
Understanding Endpoint Security: Endpoint protection, also called endpoint security, is the practice of securing end-user devices from cyber threats and malicious activities. These devices are potential entry points for cybercriminals, making endpoint protection a...

Mar 29, 2023 | News, Uncategorized
Many businesses encounter a range of IT problems daily, from minor issues such as a malfunctioning monitor to more significant problems. Creating a plan to deal with all such issues that arise isn’t necessarily a simple task for business owners or managers but there...

Sep 27, 2022 | News, Cyber Security
We live in a technologically centred world where all our data is stored online – from your latest online shopping spree to the holiday you just booked – everything you share, post and search remains online. Due to this, laws regarding data privacy and...
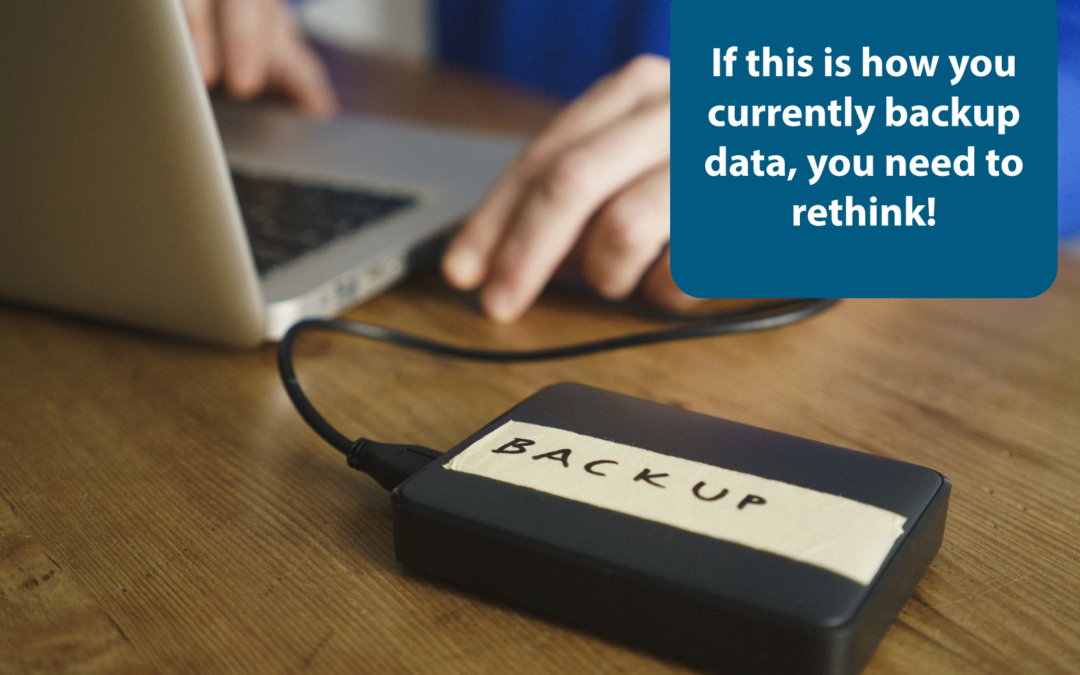
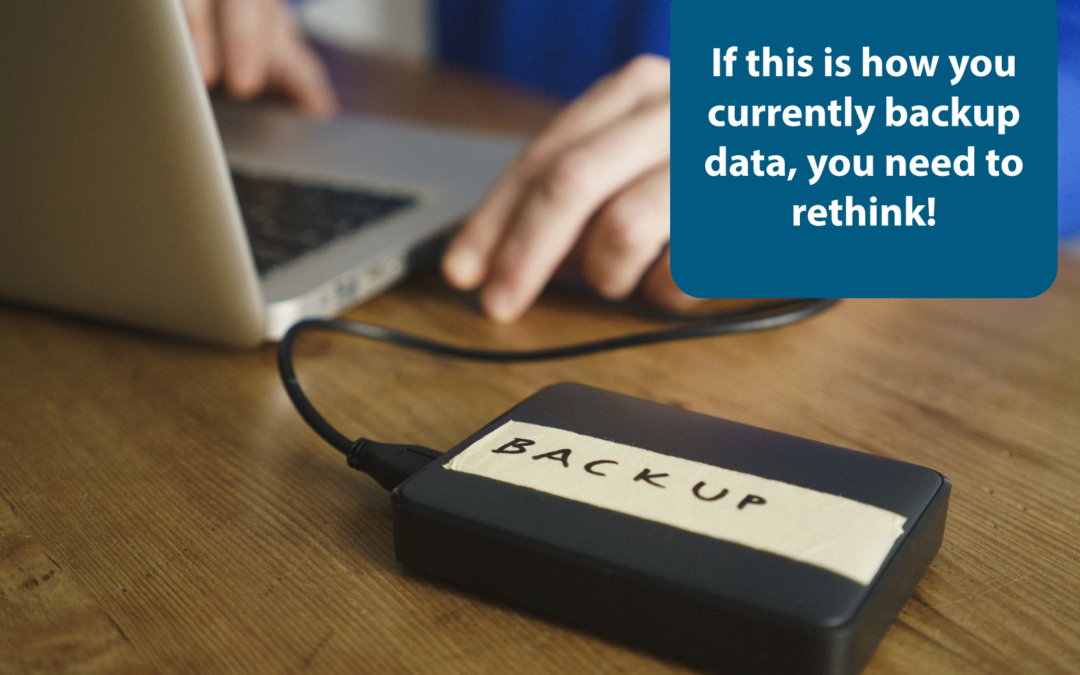
May 20, 2022 | News, Cyber Security
No matter how robust your IT systems are, they are under constant threat of disruption and downtime. Ransomware and other cyberattacks, power outages, equipment failures, and natural disasters can all take your IT systems out of the game. However, a robust managed...